ソフトウェアとハードウェアのハッキングの比較
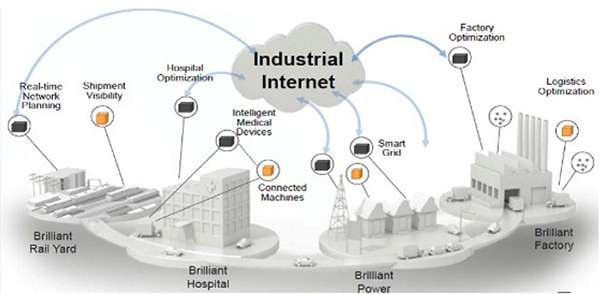
暗号化は、ハードウェアでもソフトウェアでも、セキュリティ違反を最小限に抑え、保護レイヤを追加してデータを保護します。一方で、ハードウェアとソフトウェアでは暗号化を使用する状況とその理由に違いがあるのが一般的です。
ソフトウェアの暗号化は、コスト効率の良さ、アップグレード/更新のしやすさから、組織のデバイスを保護するのが一般的です。また、保存済み、格納済み、および転送中のデータを保護するために、この暗号化は、暗号化を強化および補完する機能でサポートされることがよくあります。
それに対し、ハードウェアベースの暗号化はデバイスのオンボードセキュリティにあり、暗号化と復号化を実行し、ソフトウェアを追加することなく、汚染、悪意のあるコードへの感染、脆弱性を排除します。この暗号化はポータブルデバイス上の機密データを保護するために最も使用され、維持されているデータも保護します。機密データが含まれるドライブは、ドライブが盗まれた場合でもデータを保護するハードウェアキーを通じて保護することができます。ハードウェアソリューションは、コストが大幅に節約されるソフトウェアのアップグレード/更新を実行する場合に比べ、コストがかかり、ハードウェアプラットフォームへのアップグレードが必要です。
ソフトウェアの脆弱性
今世紀に入って20年が経過した今でも、データを適切に保護していない企業が存在することを指摘しなければなりません。更新、アップグレード、またはパスワードを変更していない、複数の保護方法を採用していない、そしてよくあるのが、ネットワークに接続するデバイスでデフォルトのパスワードコードを変更していないなどです。このようなハッカーにとってのローハンギングフルーツが作成されるのは、簡単に回避できるセキュリティの脆弱性が大きな割合を占めていることを表します。
他にも次のような脆弱性があります(ただし、これらに限定されません)。
- 保存データに対して強力な暗号化を使用していない
- 特にバッファオーバーフローに対して脆弱なC/C++で記述されたモバイルアプリで、メモリの容量に対し保存データの量が多すぎる
- 安全でないサービスやAPIを通じてデータに直接アクセスしている
- ログファイルへのアクセスを制御せず、ハッカーはセキュリティの脆弱性を明らかにできる
- 他のソースから企業に寄生的コードを持ち込む可能性のあるコードの再利用
- パストラバーサルを使用し、ドットドットスラッシュ攻撃を作成するハッカー
- 攻撃者がウェブサイトのビジターのブラウザでコードを実行するクロスサイトスクリプティング
- ログイン以外の認証が不十分
ハードウェアの脆弱性
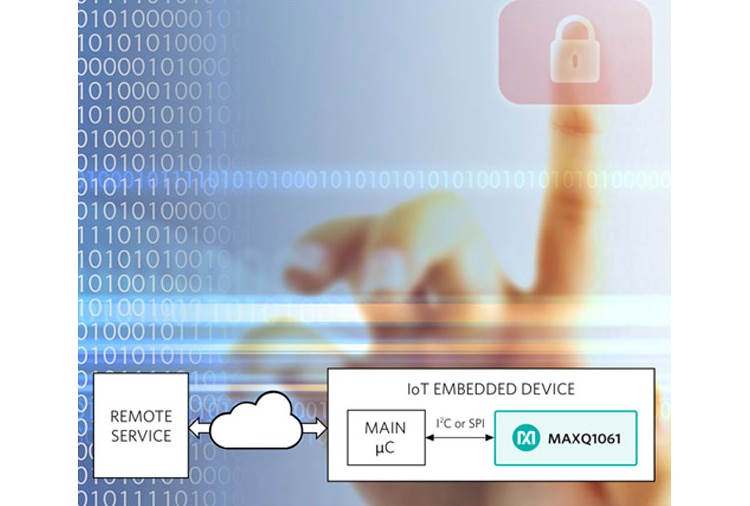
ハードウェアの脆弱性は、多くの場合、回路がどの程度攻撃からプライベートキーを保護する設計になっているかによります。攻撃が成功する理由は次のとおりです(ただし、この場合もこれらに限定されません)。
- 電磁サイドチャンネル攻撃での電磁波の傍受
- セキュアなデバッグ機能でMCUを使用していない
- 改ざん条件を含み、改ざんが生じたときにメモリからプライベートキーを削除する改ざん防止手法を作成していない
- セキュアブートを確実に行っていない
対応可能なソリューション
さまざまなセキュリティベースのソリューションが販売され、その数は増え続けています。ここでは、検討すべきいくつかの推奨ソリューションを示します。ハードウェアベースのセキュリティコアを使用します。たとえば、Silicon LabsのWireless Gecko Series 2には、統合型のセキュリティコアが備わっています。最近発表されたこのテクノロジについては、ファーストルックビデオをご覧ください。
SAMD21-XPROおよびAT88CKSCKTSOIC-XPROソケットボードと暗号認証サンプルデバイスを備えるMicrochipのCryptoAuthentication SOIC XProスターターキットを検討してください。MicrochipのCypto Evaluation Studio(ACES)とこのキットを併用すると、ATECC608A、ATECC508A、ATECC108A、 ATSHA204A、およびATAES132Aを含むすべての暗号認証デバイスをサポートできます。
これもMicrochipの製品ですが、AWSゼロタッチセキュアプロビジョニングキットは、AWS IoTデバイスのプロビジョニング用の完全な開発および試作プラットフォームを備えています。図1に示すように、このキットには3つのカスタマイズされた(ATCRYPTOAUTH-XAWS)アドオンボードが含まれ、それぞれのボードには、キットの署名者スクリプトによる現場プロビジョニング用にAWSで構成されたECC508が含まれています。また、セキュアルートおよび署名者プロビジョニングスクリプトも含まれています。このキットはモジュール式のXplained PROプラットフォームに基づいており、さまざまなプロセッサ、コネクティビティ、およびヒューマンインタラクティビティインターフェースモジュールを試すことができます。
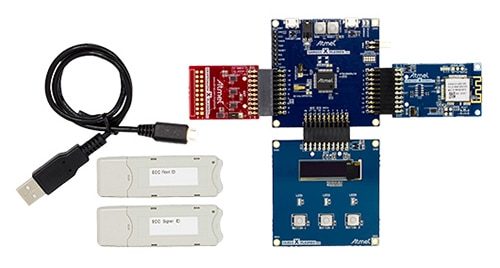 図1:MicrochipのAWSゼロタッチセキュアプロビジョニングキットは、新しいAWSセキュリティ規制に準拠するIoTデバイスの高速かつ簡単な設計を実現します。(画像提供:Microchip)
図1:MicrochipのAWSゼロタッチセキュアプロビジョニングキットは、新しいAWSセキュリティ規制に準拠するIoTデバイスの高速かつ簡単な設計を実現します。(画像提供:Microchip)
NXPのOM-SE050ARD開発キットを使用して、SE050製品ファミリの機能を評価し、セキュアなIoTアプリケーションの開発を簡素化できます(図2)。IoTデバイスのセキュアなEdgeLock要素は、ICレベルで信頼の基点を提供し、セキュリティコードを記述することなく、エッジからクラウドまで真のエンドツーエンドセキュリティを実現します。
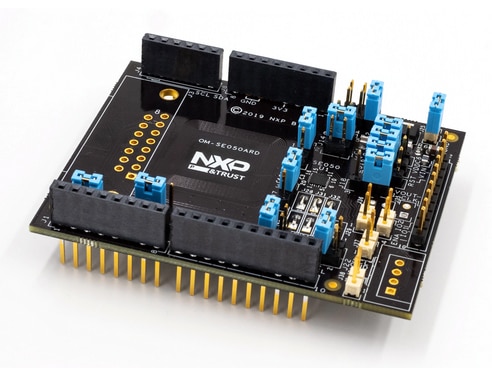 図2:NXPのOM-SE050ARDは、EdgeLock SE050ファミリ製品向けの柔軟で簡単な開発キットです。(画像提供: NXP)
図2:NXPのOM-SE050ARDは、EdgeLock SE050ファミリ製品向けの柔軟で簡単な開発キットです。(画像提供: NXP)
設計を保護するのに役立つもう1つのキットは、Infineon TechnologiesのBlockchain Security 2Goスターターキットです。このキットを使用すると、クラス最高のセキュリティを迅速かつ簡単に構築できます。このキットには、セキュアキーの生成にすぐに使用できるNFCカード、署名方式、ピン保護、キー管理のコマンドをサポートするオンカードソフトウェア、署名の作成とPIN認証およびInfineonのブロックチェーンハブへのアクセスが含まれています。対応するブロックチェーンアプリケーションの1つが、認証システムの基盤として使用されるID管理です。
攻撃は非常に一般的で高度になってきています。ソフトウェアおよびハードウェア両方の領域で保護を開始し、最初にすばやく攻撃を受けるローハンギングフルーツにならないようにしてください。その後、最も脆弱な場所を検討して、利用しやすくなっているオプションを確認してください。
Have questions or comments? Continue the conversation on TechForum, Digi-Key's online community and technical resource.
Visit TechForum