長期的なCRAコンプライアンスのための安全なハードウェア基盤の構築方法
DigiKeyの北米担当編集者の提供
2026-04-08
欧州連合(EU)のサイバーレジリエンス法(CRA)により、サイバーセキュリティは、単なる付帯的な考慮事項から、デジタル要素を含む製品における中核的なアーキテクチャ上の課題へと根本的に変化しました。2027年から規制の完全施行が始まるため、開発者はこの法律に基づく自らの責任を認識しておく必要があります。そうすることで、組み込み製品のライフサイクル全体を通じて、これらの責任を果たすために適切な処理用ハードウェアを選択できるようになります。適切なハードウェアを採用することで、たとえばOTA(Over-the-Air)アップデートによる継続的な脆弱性管理をサポートする、セキュアバイデザインのアーキテクチャを実現できます。
本記事では、CRAの要件について簡単に概要を説明し、機密データの隔離や、デバイスの完全性を保証するハードウェアルートオブトラスト(RoT)の管理を行い、デバイスの完全性を確保するための基盤として、セキュアエンクレーブ技術について解説します。続いて、CRA準拠のソリューションの基盤となるNXP Semiconductorsのマイクロコントローラユニット(MCU)およびアプリケーションプロセッサを紹介し、その実用的な実装例を紹介します。
変化するサイバーセキュリティの義務
CRAの下では、メーカーがコンプライアンスを確保するための法的責任をすべて負います。要約すると、CRAはメーカーに対し、以下のことを求めています。
- デバイスを改ざんから保護し、初回起動時からソフトウェアの完全性を保証すること
- 継続的な脆弱性管理と定期的なセキュリティ更新を含む、少なくとも5年間、または製品の予想寿命がそれより短い場合はその期間にわたり、サポート期間を提供すること
- 更新プログラムに入手可能性と最新の技術文書を10年間、またはより長いサポート期間にわたって維持すること
- 製品の市場投入時に、サポート終了日を明示すること
- 実際に悪用されたセキュリティ脆弱性を、24時間以内に国家コンピュータセキュリティインシデント対応チーム(CSIRT)および欧州連合サイバーセキュリティ機関(ENISA)に報告し、72時間以内に詳細な報告を行い、14日以内に最終報告を行うこと
- CRAの「重要」(クラスIおよびクラスII)および「極めて重要」の指定を受けた専門製品について、第三者認証を提供すること
- メーカーがEU市場へのアクセスに際して欧州適合(CE)マークを使用することを認める、正式な適合宣言書(DoC)に署名すること
CRAの必須要件の中核をなすのは、すべての製品に対して安全なハードウェア基盤を確立することから始まり、デバイスの完全性を確保し維持するという取り組みです。CRAは具体的なフレームワークを定義していませんが、セキュアエンクレーブ技術は、設計者がこの必須要件を確実に管理するための信頼できる方法を提供します。
セキュアエンクレーブ技術がファームウェア認証をサポートする方法
通常、より大規模なシステムオンチップ(SoC)に組み込まれるセキュアエンクレーブ(図1)は、ソフトウェア検証資産(暗号鍵など)を生成、保存、管理し、システムにハードウェアRoTを提供するセキュアなハードウェアサブシステムです。これらのリソースをデバイスの他の部分から隔離することで、開発者は不正アクセスから保護することができます。これにより、セキュアブートプロセスを使用して、システム全体を不正なソフトウェアから保護することが可能になります。
 図1:セキュアエンクレーブは、ハードウェアRoTを確立し、これに基づいてブートプロセスの各段階の正当性を検証することで、システムの完全性を確保します。(画像提供:Brandon Lewis氏)
図1:セキュアエンクレーブは、ハードウェアRoTを確立し、これに基づいてブートプロセスの各段階の正当性を検証することで、システムの完全性を確保します。(画像提供:Brandon Lewis氏)
起動はセキュアなエンクレーブ内で開始され、そこでRoTがセキュアなファームウェアの起動の各段階で署名を検証し、セキュアサブシステムが侵害されていないことを確認します。もし不一致がある場合、RoTはブートシーケンスの完全性を検証できないため、ブートプロセスは停止します。これが、メインシステムを改ざんから保護するための第一段階となります。
その後の各ブート段階において、セキュアエンクレーブは、ハードウェアRoTに固定された公開鍵を使用して署名を検証します。この検証により、メーカー署名付きのコードのみが実行されることが保証されます。したがって、いずれかの段階で検証が失敗した場合、メインシステムは起動を中止するか、機能を制限した状態で実行され、それによって潜在的な脅威を封じ込めます。
長期的なCRAコンプライアンスには、製品のライフサイクルを通じて定期的な更新も必要となるため、各パッチが正規のものであることを検証する上で、セキュアブートは不可欠です。これは、インストールが自動で行われることが多いOTAアップデートにおいて、特に重要な意味を持ちます。セキュアエンクレーブは、セキュアブートの信頼の連鎖における基盤となる要素を提供します。したがって、開発者は、このサブシステムを備えた高度なハードウェアコンポーネントの恩恵を受けることができます。
セキュリティバイデザインをサポートする高性能MCU
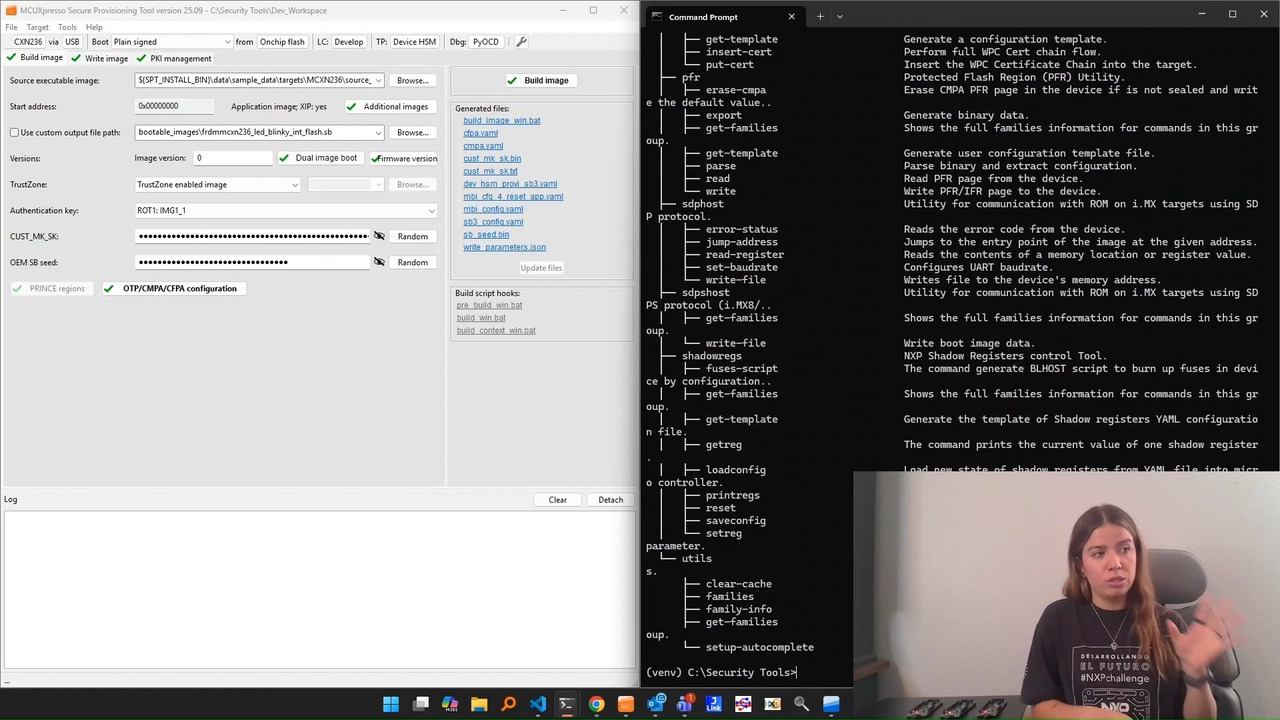
CRAに準拠した製品を構築する場合、NXPのMCX NシリーズMCU(図2)は、エッジAI処理向けのニューラルプロセッシングユニット(NPU)を統合したデュアルArm®Cortex®-M33アーキテクチャに加え、専用のセキュアなサブシステムを提供します。1メガヘルツあたり57マイクロアンペア(μA/MHz)という低消費電流動作により、バッテリ駆動設計での長寿命化を実現し、さらに消費電流を最小2μAまで低減するパワーダウンモードも備えています。
NXP EdgeLockセキュアサブシステムは、セキュアエンクレーブとして機能します。ハードウェアの悪用を防ぐためのグリッチおよび改ざん検知モジュールに加え、EdgeLockサブシステムは、ソフトウェアの完全性を維持するための以下のような対策が取られています。
- 不正アクセスを防ぐデバッグ認証機能
- 公開鍵暗号(PKC)。これには、暗号化用のAES-256およびECC-256モジュール、暗号ハッシュ用のSHA-512、および低レイテンシブロック暗号用のPRINCEモジュールを搭載
- デバイス固有の識別子を生成し、不変のハードウェアRoTをサポートするための鍵を導出するための、SRAMベースのクローン不可能機能(PUF)
 図2:CRA準拠のEdgeLockセキュアサブシステムに加え、NXP MCX N94x MCUは、多種多様なアプリケーションに対応するための幅広いインターフェースを備えています。(画像提供:NXP)
図2:CRA準拠のEdgeLockセキュアサブシステムに加え、NXP MCX N94x MCUは、多種多様なアプリケーションに対応するための幅広いインターフェースを備えています。(画像提供:NXP)
さらなる保護機能として、MCX N94x MCUは、セキュアな実行環境を実現するArm TrustZoneと、時間ベースのセキュリティメカニズムを保護する改ざん防止ピンを備えたリアルタイムクロック(RTC)を搭載しています。また、メモリの悪用を防ぐために、セキュアなダイレクトメモリアクセス(DMA)コントローラ、メモリ保護ユニット(MPU)、および誤り訂正符号(ECC)メモリも搭載されています。MCX N94x MCUには、2つのバリエーションがあり、開発者は特定のアプリケーションに合わせてメモリ要件を調整できます。MCXN946VDFTは、184ピンのVFBGAパッケージに1メガバイト(Mバイト)のフラッシュメモリと352キロバイト(Kバイト)のSRAMを統合しており、一方、MCXN947VDFTは、172ピンのHDQFPパッケージに2Mバイトのフラッシュと512KバイトのSRAMを搭載しています。
MCX N94x MCUは、セキュリティおよびメモリ機能に加え、デジタルおよびアナログI/O、ヒューマンマシンインターフェース(HMI)、モータ制御サブシステムを提供します。-40°C~+125°Cの動作温度範囲と組み合わせることで、産業用オートメーション機器、スマート家電、電動工具、医療機器など、CRA準拠の多様な製品設計を可能にします。
MCX N94x MCUを用いたアプリケーションを開発において、FRDM-MCXN947評価ボード(図3)は効果的な出発点となります。EthernetやUSB Type-Cポート、拡張ヘッダなど、豊富な接続オプションを備えており、使い慣れたツールを用いた迅速なアプリケーション開発を可能にします。また、NXPは拡張ボードハブやアプリケーションコードハブなどのリソースを提供しており、互換性のあるハードウェア測定やMCUXpressoを使用したプログラミングにおいて、開発チームを支援します。
 図3:FRDM-MCXN947評価ボードは、CRA準拠システムの迅速な試作を可能します。(画像提供:NXP)
図3:FRDM-MCXN947評価ボードは、CRA準拠システムの迅速な試作を可能します。(画像提供:NXP)
組み込みLinuxアプリケーション向けNXP EdgeLock
NXPは、電力効率に優れたアプリケーションプロセッサi.MX 93シリーズ(図4)にもEdgeLockセキュアエンクレーブを搭載しています。これらは、MCX N94x MCUと同等の高性能周辺機器を備えつつ、単一のCortex-M33コアと2つのLinux対応Arm Cortex-A55アプリケーションコアを組み合わせた構成となっています。
 図4:i.MX 93アプリケーションプロセッサは、EdgeLockとCortex-M33および2つのCortex-A55コアを組み合わせることで、組み込みLinuxシステムのセキュアな基盤を提供します。(画像提供:NXP Semiconductors)
図4:i.MX 93アプリケーションプロセッサは、EdgeLockとCortex-M33および2つのCortex-A55コアを組み合わせることで、組み込みLinuxシステムのセキュアな基盤を提供します。(画像提供:NXP Semiconductors)
MCX N94x MCUと同様に、i.MX 93アプリケーションプロセッサのEdgeLockセキュアエンクレーブには、改ざん検知機能と暗号化モジュールが搭載されています。しかし、専用のセキュアクロック(時間ベースの攻撃を防ぐために搭載)と電子ヒューズによる暗号鍵の格納領域も、ハードウェアRoTとして機能します。また、より広いシステムメモリはリアルタイムサブシステム内のECC RAMとMPUによって保護されています。Cortex-AコアとCortex-Mコアの両方に、セキュアなソフトウェアパーティショニングのためのArm TrustZoneを備えており、高信頼性リソースドメインコントローラ(TRDC)によってさらにサポートされています。
NXPは、民生用、車載用、産業用の温度範囲に対応したi.MX 93デバイスを製造するだけでなく、幅広いアプリケーション向けにスケーラブルなコンピューティングオプションも提供しています。たとえば、MIMX9351DVVXMABは、最大1.7ギガヘルツ(GHz)で動作する単一のCortex-A55コアと、スマートホームハブなどの高性能エッジAIアプリケーションをサポートするNPUを搭載しています。一方、MIMX9302DVVXDABは、最大900MHzで動作する2つのCortex-A55コアを搭載し、オプションのNPUを省略しているため、デジタル情報キオスクやマルチカメラセキュリティシステムに適した汎用コンピューティングソリューションとなっています。これらのリソースには、他にもさまざまなバリエーションも用意されています。
i.MX 93アプリケーションプロセッサを用いた開発を加速するために、MCIMX93-QSB評価ボード(図5)には、プログラミング、ネットワーク接続、およびシステム拡張のための複数のコネクタが搭載されています。これには、EthernetおよびUSB Type-Cポート、拡張ヘッダ、M.2 Key-Eスロットが含まれています。このボードは、i.MXソフトウェアおよび開発ツールによってサポートされています。
 図5:MCIMX93-QSB評価ボードおよびサポートソフトウェアにより、i.MX 93アプリケーションの開発が加速されます。(画像提供:NXP Semiconductors)
図5:MCIMX93-QSB評価ボードおよびサポートソフトウェアにより、i.MX 93アプリケーションの開発が加速されます。(画像提供:NXP Semiconductors)
CRAのサポート期間に関するコミットメントに沿ってデバイスのセキュリティをさらに強化するため、NXPのEdgeLock 2GOクラウドサービスは、デバイスのライフサイクル全体を通じて、開発者に安全なOTAアップデート、コード署名、証明書と鍵の管理を提供します。EdgeLockで保護されたデバイスに標準で統合されることで、長期的なCRAコンプライアンスをサポートする包括的なセキュリティ戦略の基盤を完成させます。
まとめ
EUのCRAは、今後数年にもわたりデジタル製品の開発を形作ることになりますが、開発者は期限に間に合わせるために、今すぐこれを理解する必要があります。CRAに準拠した製品を設計する場合、NXPのMCX N94x MCUやi.MX 93アプリケーションプロセッサなどのデバイスは、EdgeLockセキュアエンクレーブおよび追加のハードウェアセキュリティ対策を通じて、堅牢なハードウェアセキュリティ基盤を提供します。EdgeLock 2GOを活用することで、開発チームは、この変化し続ける規制環境において、長期的なCRAコンプライアンスとセキュアバイデザイン製品への取り組みをさらに強化することができます。

免責条項:このウェブサイト上で、さまざまな著者および/またはフォーラム参加者によって表明された意見、信念や視点は、DigiKeyの意見、信念および視点またはDigiKeyの公式な方針を必ずしも反映するものではありません。