A Simple Solution Simplifies Authentication to Ensure Device Security
Contributed By DigiKey's North American Editors
2018-06-21
The ability to authenticate data or operations in a system is a fundamental requirement for security. For developers, implementing the detailed steps required for authentication can be challenging, particularly in resource constrained systems. Even when resources are available, time to market pressures and lack of awareness can result in shortcuts during development that can leave the final system compromised.
What’s required is a fundamental understanding of how authentication works, and a solution for developers that incorporates both the required resources as well as the support to implement authentication much faster and effectively.
This article will discuss the basics of symmetric and asymmetric authentication before introducing dedicated authentication ICs from Maxim Integrated. The article will then discuss how to use these ICs to easily add support for industry standard authentication mechanisms. These mechanisms are needed to ensure use of authorized devices in applications such as the Internet of Things (IoT), secure firmware update in systems, and connection of authorized peripherals, just to mention a few.
The critical role of authentication
Authentication remains one of the core requirements for security, and finds applications across nearly every segment including consumer, industrial, medical, mil/aero, and more. On the Web, authentication is used in browsers to validate the identity of secure (https) servers. In IoT devices, authentication is critical for ensuring that firmware updates only come from legitimate sources. On a smaller scale, authentication is used increasingly to ensure use of authorized peripherals or even consumables in systems where mismatches can impact power, safety, and reliability.
Authentication serves a particularly vital role in connected applications, where an unauthorized device can serve as an entry point for hackers to attack the application at large and its underlying system resources. In mission critical applications, the need for authentication becomes particularly acute.
For example, an unauthorized sensor device connected by accident or by intention to an industrial automation network could affect data streams used in process control loops. In these applications, the need for authentication goes both ways. After authenticating itself to a host, a device that operates actuators, lasers, or other external equipment should operate only after authenticating commands that could result in physical harm or damage.
Authentication methods
Authentication methods differ widely. In its simplest and most common form, individuals use a password to authenticate themselves to systems and applications. This notoriously weak form of authentication has driven the use of two-factor authentication or biometric methods such as Apple Touch ID fingerprint recognition or Windows Hello facial recognition.
In digital systems, however, authentication builds on a basic mechanism where a host issues a "challenge" and validates the "response" of an IoT device, peripheral, or consumable. In this approach, the challenged device constructs a valid response using a secret key that is shared or not shared with the host in symmetric cryptography authentication or asymmetric cryptography authentication, respectively.
In symmetric cryptography authentication, the slave device and host each compute a digital signature based on a SHA-256 hash of the challenge data, a shared secret key, and other data elements. If the slave response and host computed result match, the slave device is considered authenticated (Figure 1).
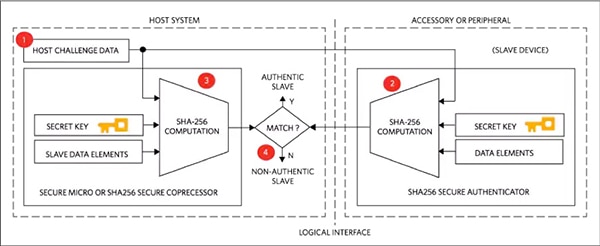
Figure 1: In symmetric cryptography, the host and slave device use a shared secret key for authentication. (Image source: Maxim Integrated)
In asymmetric cryptography authentication, the secret key resides only in the slave device, which combines it with an SHA-256 hash of the challenge data and a random number to generate a new Elliptic Curve Digital Signature Algorithm (ECDSA) signature, typically based on the elliptic-curve cryptography (ECC) P-256 curve. In turn, the host verifies the new ECDSA signature using an SHA-256 hash of the challenge data and the public key associated with the device's private key. If the result is valid, the slave device is considered authenticated (Figure 2).
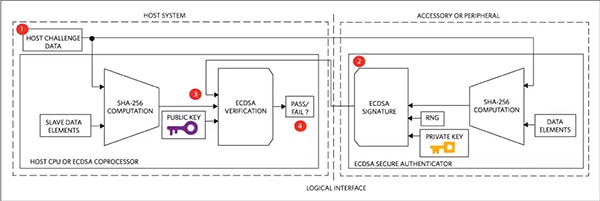
Figure 2: Asymmetric cryptography authentication eliminates vulnerabilities associated with use of a shared secret key, using a private key in the slave device and associated public key in the host for Elliptic Curve Digital Signature Algorithm (ECDSA) verification. (Image source: Maxim Integrated)
For developers, implementation of these authentication methods can be challenging to say the least. Failure to execute the precise sequence of operations with the required data can result in failure. The lack of a true random number generator or just a simple mistake can leave an otherwise secure device open to attack. Even technically correct implementations can present vulnerabilities to skilled hackers. For example, a commonly used authentication protocol permits reuse of secret information, even though those secrets could be captured and used to respond correctly to authentication challenges – and so compromise communications and connected systems.
In many cases, mistakes or vulnerabilities arise from shortcuts used to implement authentication due to a lack of robust mechanisms that are able to perform authentication more rapidly and reliably. For example, the authentication vulnerability mentioned above typically arises when developers are concerned about performance and reuse secrets rather than incur delays associated with (relatively) slow authentication execution.
In the IoT, developers might face practical limitations that simply make implementation impossible, or invite use of shortcuts that introduce vulnerabilities. The MCUs used in IoT sensor or actuator devices might lack the processor horsepower and memory resources required to implement authentication correctly or at all. The problem becomes even more evident in peripherals or consumables that lack an MCU entirely. The emergence of integrated authenticators such as Maxim Integrated’s DS28C36 and DS28E38 has significantly eased the complexity of employing authentication in any system.
Authentication ICs
The Maxim DS28C36 and DS28E38 are authentication ICs that provide drop-in solutions for challenge-response authentication. Along with 8 Kbits of secure EEPROM for private keys, private/public key pairs, certificates, and application data, the DS28C36 also integrates on-chip engines for SHA-256 and ECC-P256 cryptography. These support both symmetric and asymmetric authentication mechanisms. The device can also dynamically generate private/public key pairs for use in higher level authentication protocols.
With its comprehensive set of crypto engines, storage, and algorithm support, the device can turn complex authentication processes into a simple go/no-go result. For example, to verify firmware for MCU secure boot, developers need only program the MCU to send the target firmware and signature to a DS28C36 connected via an I2C interface. The DS28C36 in turn performs the complete sequence of operations required for authentication and returns a go/no-go result to an MCU GPIO pin (Figure 3).
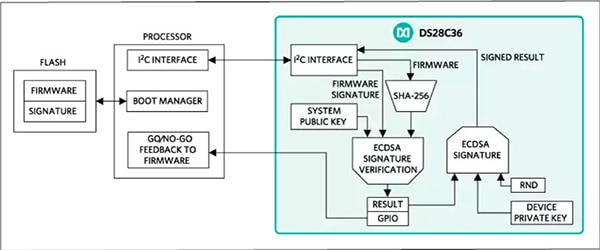
Figure 3: The Maxim Integrated DS28C36 implements the complete authentication challenge-response mechanisms, enabling developers to use it to provide a simple go/no-go result for firmware verification in secure boot operations. (Image source: Maxim Integrated)
Developers can use the DS28C36's programmable I/O pins to support command authentication in applications where activation of a laser, relay, or other actuator can result in potential hazards in the physical environment. Here, developers could drive the go/no-go result of the authentication process to a DS28C36 output pin controlling a buffer transistor such as the Nexperia PMV65XP MOSFET driving a laser (Figure 4). With this approach, only valid commands would be allowed to control the peripheral.
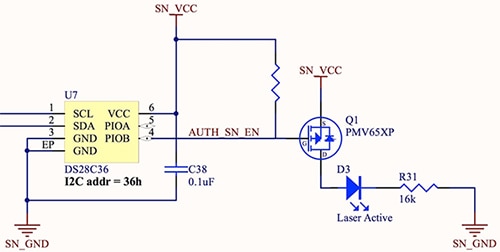
Figure 4: Developers can use the Maxim Integrated DS28C36 to authenticate peripheral operations, even directly enabling output drivers using its programmable I/O ports to convey the result of the authentication process. (Image source: Maxim Integrated)
For some applications, however, the need to load secret keys into an authentication IC would be a potential security weakness for mission critical devices, or simply too cumbersome for volume products such as consumables like printer cartridges. For any application, the mere presence of the secret key that controls access to a product causes the product and underlying authentication device to become the target of hackers looking to recover the key through more sophisticated attack mechanisms.
Physically unclonable function
The Maxim DS28E38 authentication IC provides a unique approach to mitigating key threats by providing a built-in key based on Maxim’s patented ChipDNA™ technology. ChipDNA uses the random variations in semiconductor device characteristics to provide a physically unclonable function (PUF). The PUF feature is used to create a unique secret key that remains constant over time and under different operating conditions, including operating voltage and temperature. The only way the PUF output (and resulting key) changes is if someone attempts to probe low level chip operations. Such operations change underlying circuit characteristics, resulting in a different PUF output and a different secret key. It’s a kind of “Heisenberg Uncertainty Principle,” but applied to secret key storage. For applications that require a specific private key, the device nevertheless allows developers to load and use their own keys instead.
The PUF-based DS28E38 integrates a complete set of security features to provide a turnkey challenge-response authentication solution. Unlike the DS28C36, however, the DS28E38 supports only asymmetric authentication, returning an ECDSA signature in response to a challenge (Figure 5). The host remains responsible for using the device's ECDSA signature with the corresponding public key to complete the pass/fail verification process as illustrated earlier in Figure 2.
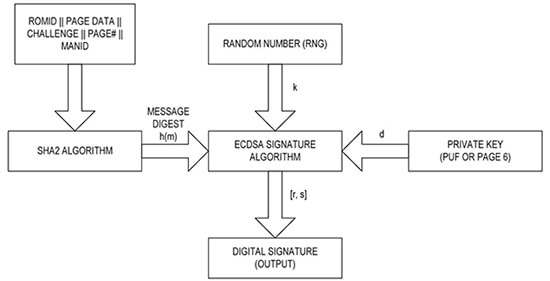
Figure 5: The Maxim Integrated PUF-based DS28E38 authentication IC implements the complete sequence of asymmetric cryptography authentication, generating a digital signal response to a challenge provided by the host. (Image source: Maxim Integrated)
Besides the PUF-based secret key, the device provides 2 Kbits of secure EEPROM storage, as well as a separate unique 64-bit identifier (ROM ID) and manufacturing identifier (MANID). Using the device's secret key, unique identifiers, and secure storage, developers can use the DS28E38 in a wide variety of authentication scenarios.
For example, to authenticate a printer cartridge, developers could authenticate the cartridge with known values of the MANID to confirm a model type. As with the DS28C36, developers can use the DS28E38 to dynamically generate private/public key pairs to support more complex authentication protocols.
Flexible interface
For hardware integration, the DS28E38 provides a 1-Wire interface, enabling a simple connection directly with MCUs such as the MAX32625 that include native 1-Wire support. For other MCUs, developers can connect the device to an MCU programmable I/O (PIO) port using a single PMV65XP MOSFET (Figure 6).
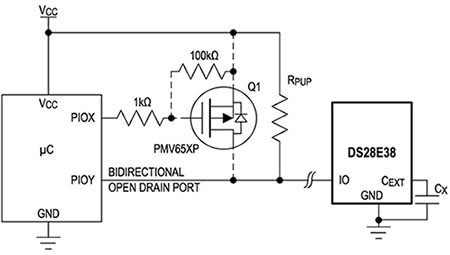
Figure 6: The DS28E38 1-Wire interface provides a simple connection to 1-Wire MCUs such as the Maxim MAX32625 and requires only an additional MOSFET to interface to a programmable I/O port on any MCU. (Image source: Maxim Integrated)
1-Wire waveform timing requirements are well within the performance of even simple MCUs. As a result, developers can implement the 1-Wire protocol with a few lines of software (Listing 1).
Copy
//-----------------------------------------------------------------------------
// Send a 1-Wire write bit. Provide 10us recovery time.
//
void OWWriteBit(int bit)
{
if (bit)
{
// Write '1' bit
outp(PORTADDRESS,0x00); // Drives DQ low
tickDelay(A);
outp(PORTADDRESS,0x01); // Releases the bus
tickDelay(B); // Complete the time slot and 10us recovery
}
else
{
// Write '0' bit
outp(PORTADDRESS,0x00); // Drives DQ low
tickDelay(C);
outp(PORTADDRESS,0x01); // Releases the bus
tickDelay(D);
}
}
//-----------------------------------------------------------------------------
// Write 1-Wire data byte
//
void OWWriteByte(int data)
{
int loop;
// Loop to write each bit in the byte, LS-bit first
for (loop = 0; loop < 8; loop++)
{
OWWriteBit(data & 0x01);
// shift the data byte for the next bit
data >>= 1;
}
}
Listing 1: Developers can implement the 1-Wire protocol with a few lines of code to drive an MCU programmable I/O port high and low using MCU dependent delay values (A, B, C, and D) needed to match 1-Wire protocol waveform timing specifications. (Code source: Maxim Integrated)
Alternatively, developers can connect the DS28E38 to a standard MCU I2C port using a DS2484 1-Wire interface device, allowing developers to work with familiar I2C I/O techniques in their designs. This approach is particularly attractive in IoT device designs that require additional peripherals (Figure 7).
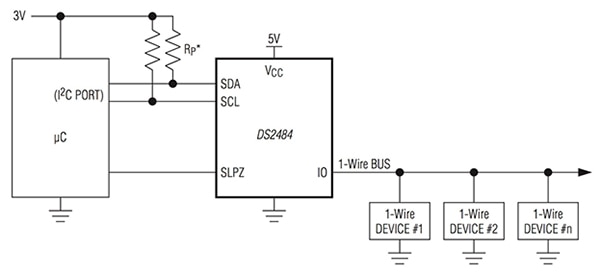
Figure 7: Developers building systems with multiple 1-Wire devices can use the Maxim DS2484 to connect the DS28E38 authentication IC with other 1-Wire devices to an MCU's I2C bus. (Image source: Maxim Integrated)
With the DS2484, developers can use the DS28E38 in combination with a broad array of available 1-Wire devices including sensors, battery management ICs, EEPROMs, and more. In this configuration, developers can easily use the DS28E38 to provide authentication for critical operations involving those 1-Wire peripheral devices similar conceptually to that shown in Figure 4 for a DS28C36-based design.
Rapid development
Although both the DS28C36 and DS28E38 present simple hardware interface requirements, the real effort in incorporating authentication in a design lies in building these mechanisms into higher level processes and applications. To accelerate this process along, Maxim provides a number of evaluation kits that designers can use to quickly gain experience with the functionality of the DS28C36 and DS28E38 authentication ICs. To evaluate the DS28C36, connect to the MAXAUTHDEMO1# evaluation board via USB (Figure 8).
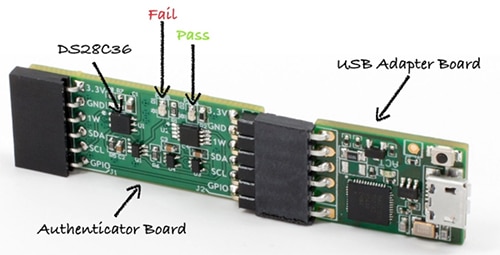
Figure 8: The Maxim MAXAUTHDEMO1# USB evaluation board allows developers to quickly explore functionality of the DS28C36 and easily see the pass/fail results of specific authentication operations with the built-in LEDs. (Image source: Maxim Integrated)
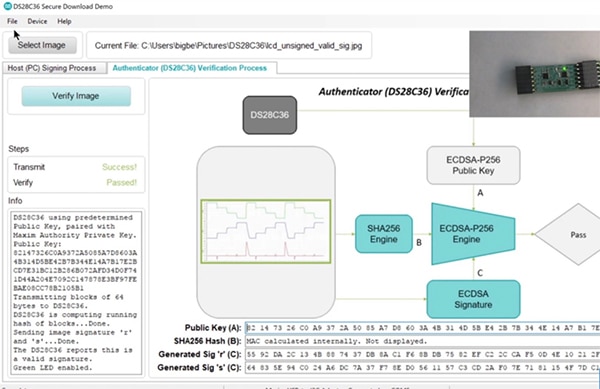
An accompanying DS28C36 secure download software program provides a basic demonstration of authentication operations. On the signing process screen, developers use the software to create a signature for a test file (image files in this case). On the second screen, they use the DS28C36 to authenticate the original file against that signature: the same process used to authenticate firmware in a secure update process (Figure 9).
Figure 9: Maxim's DS28C36 secure download demo software allows developers to experiment with host signing and DS28C36-based verification through detailed results, combining debug text output and associated data generated at each step. (Image source: Maxim Integrated)
The Maxim DS28E38EVKIT# provides a similar platform for exploring operation of the DS28E38. After plugging the DS28E38EVKIT# into a PC USB slot, running the accompanying software demonstrates authentication, key pair generation, certificate generation, and other features and functions. For further software development using the DS28E38, Maxim also provides its MAXREFDES168# software reference design for use with its MAX32625 MCU-based MAX32625MBED# MBED eval kit. Sample C++ code in the reference design demonstrates the steps used to build command sequences used to operate the DS28E38 (Listing 2).
Copy
error_code
DS28E38::computeAndReadPageAuthentication(int pageNum, bool anonymous,
const Page & challenge,
Ecc256::Signature & signature) {
if (pageNum < UserData0 || pageNum >= memoryPages) {
return make_error_code(InvalidParameterError);
}
const size_t parametersSize = 1 + Page::csize;
const size_t resultSize = Ecc256::Signature::size;
typedef array<uint_least8_t,
(parametersSize > resultSize ? parametersSize : resultSize)>
Buffer;
Buffer buffer;
buffer[0] = pageNum | (anonymous ? 0xE0 : 0x00);
copy(challenge.begin(), challenge.end(), buffer.begin() + 1);
const error_code result = runCommandSequence(
ComputeAndReadPageAuthentication, buffer.data(), parametersSize,
generateEcdsaSignatureTimeMs, buffer.data(), resultSize);
if (!result) {
Buffer::const_iterator begin = buffer.begin();
Buffer::const_iterator end = begin + signature.s.size();
copy(begin, end, signature.s.begin());
begin = end;
end = begin + signature.r.size();
copy(begin, end, signature.r.begin());
}
return result;
}
Listing 2: Maxim's MAXREFDES168# software reference design provides software examples for key operations such as building a command block for authentication shown here, as well as low level service routines able to execute a command block and other functions. (Code source: Maxim Integrated)
Conclusion
Authentication mechanisms lie at the heart of any secure environment. For developers, however, implementation of these mechanisms brings multiple challenges for meeting practical performance requirements while also maintaining security at each step of the authentication sequence.
With the emergence of dedicated authentication ICs, developers can easily address these challenges and meet emerging requirements for authentication across diverse application segments. Using these dedicated devices, engineers can quickly incorporate authentication in designs targeting applications as complex as the IoT or as simple as printer cartridges.

Disclaimer: The opinions, beliefs, and viewpoints expressed by the various authors and/or forum participants on this website do not necessarily reflect the opinions, beliefs, and viewpoints of DigiKey or official policies of DigiKey.